My beloved desktop Mac – a Mac Pro 5,1 – started exhibiting signs of an impending graphic card failure. After a few hours of use, patterns of visual artifacts made of little squares would fill the screen, the mouse curser would be replaced with text, and then the computer would become unresponsive. I could still use the various shared hard drives via other Macs on my Local Area Network, but eventually I would have to do a forced reboot1.
A hard reboot like that is not ideal for many reasons, including potentially corrupting databases like my Lightroom catalog or my DEVONThink database or other issues. Luckily, I don’t think that happened, but it certainly was a risk. Eventually the graphic card probably wouldn’t recover after a failure, so I purchased a new2 card with a GPU.
The Mac Pro 5,1 aka The Cheese Grater, is a beloved Mac because it was engineered to be opened up and upgraded. The whole side panel pops off smoothly, the internal components are accessible, and some slide out if you need them to. I miss that era, to be honest, when computers were designed to be tinkered with. The current version of Apple locks away most components from casual tinkerers like myself, which is probably why I didn’t invest more money and upgrade the entire machine to a newer, in warranty, model, but instead just repaired the soon to be broken part.
I attribute this to Steve Jobs being involved in the design of the original Mac Pro, who knows, maybe even Jony Ive gave useful ideas? Whatever, the Mac Pro 5,1 is a delightfully engineered computer.
While I was in the mode, I decided to also replace one of the four internal “spinning” hard drives with a newer SSD style drive. My plan is to use it as the boot drive, once I’ve used Shirt Pocket’s SuperDuper! to copy all of the files from my current boot drive. This is taking forever and a day because I’m a digital packrat, and foolishly started copying before culling out some fluff that I don’t need on either drive. Oh well…
Again, the new part installed in minutes because the Mac Pro 5,1 was engineered to make installing and/or replacing hard drives easy – there are drive bays which just pop out when you toggle a physical switch, then just 4 little screws to put in the new SSD, push it back into the drive bay, and Bob’s Your Uncle…
The plan is also to upgrade the Mac’s OS to Catalina3, maybe, or even just Mojave4 from High Sierra5, the currently installed OS sometime later this week. I have another SSD to install, this will hold my digital photography files and work files, replacing a “spinning” hard drive that currently is the repository for those.
Final thought, my dual monitor setup isn’t going to work right away as I have to buy yet another dongle, a somewhat rare MiniDisplay Female to HDMI Male connector. I ordered one, reluctantly, knowing I’ll probably find a dongle somewhere in my messy office a day later. ¯\_(ツ)_/¯
—–
Update 2/21/22
This turned out to be a more complicated project than anticipated because I didn’t follow the correct steps in order. I had to start over. Projects like this really makes one appreciate all the helpful information available on the internet. I was not a trailblazer in figuring this complicated process out, I’d bet most of the information was 5 or 10 years old, but still useful for me!
Here is what I did yesterday:
- Take out the Metal-supporting new graphics card, and install the old OEM card.
- The old card was a weird design for a factory installed card. It has an elongated plastic ring to the side which makes it too long, almost, to fit into the designated space. I really had to struggle to get it to fit, and as far as I can tell, there is no purpose for this design, at least for a Mac Pro 5,1. Maybe for some other computer? But weird because the card itself is short, only the sled holding the card was super long.
- the new card takes more power, luckily, there is an extra source of power just for this reason. Thanks Apple!
- Put a new HD (spinning) in sled, format, and do a fresh install of High Sierra from this Apple page. I don’t know if I really needed to do this, but I had a spare hard drive, and an empty slot to install it, so why not.
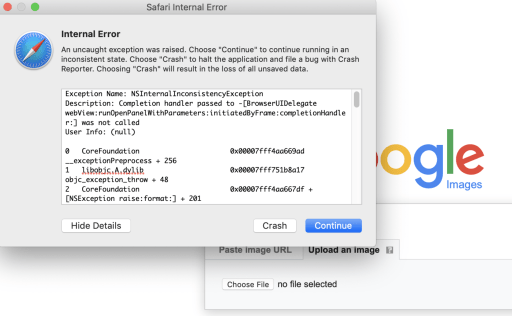
- Turn off SIP – this is where I got stuck earlier because the new graphics card doesn’t include a boot screen
- Reboot, holding ⌘-R6 to boot into Recovery Mode. This takes a moment, but eventually worked
- Load Terminal under the Utilities Menu
- Type: csrutil disable
- Reboot
- Install openCore following the simple steps7
- Remove old card, put new graphics card back in
- Update to OS Mojave via this Apple page on the new SSD drive
- Required updating firmware
- Load Install Mojave app
- Shut down
- Hold the power button for 2-3 minutes until the power light started to flash, and then a loud beep meant the firmware was updating
- I walked away, when I came back, I was at the High Sierra login screen
- Loaded the Install Mojave app again, and initiated the upgrade, easy peasy!
Right away after my first few moments in Mojave, 9 apps from the Apple App store wanted to update, plus several other apps not purchased from the Apple App store also. Yayyyy…
I may stay in Mojave for a while, looking at the Wikipedia chart of what Apple apps are included, I want to keep using iTunes instead of updating to Music. I’ve used both apps for a while now, and I still think iTunes is the better, more stable app. There is a hack to enable iTunes to be run on a newer MacOS, but I’ll wait a while for that.
Spending hours on a project like this is not wasted time, if the end result is successful. One feels a sense of satisfaction when the job is finished.
Footnotes: